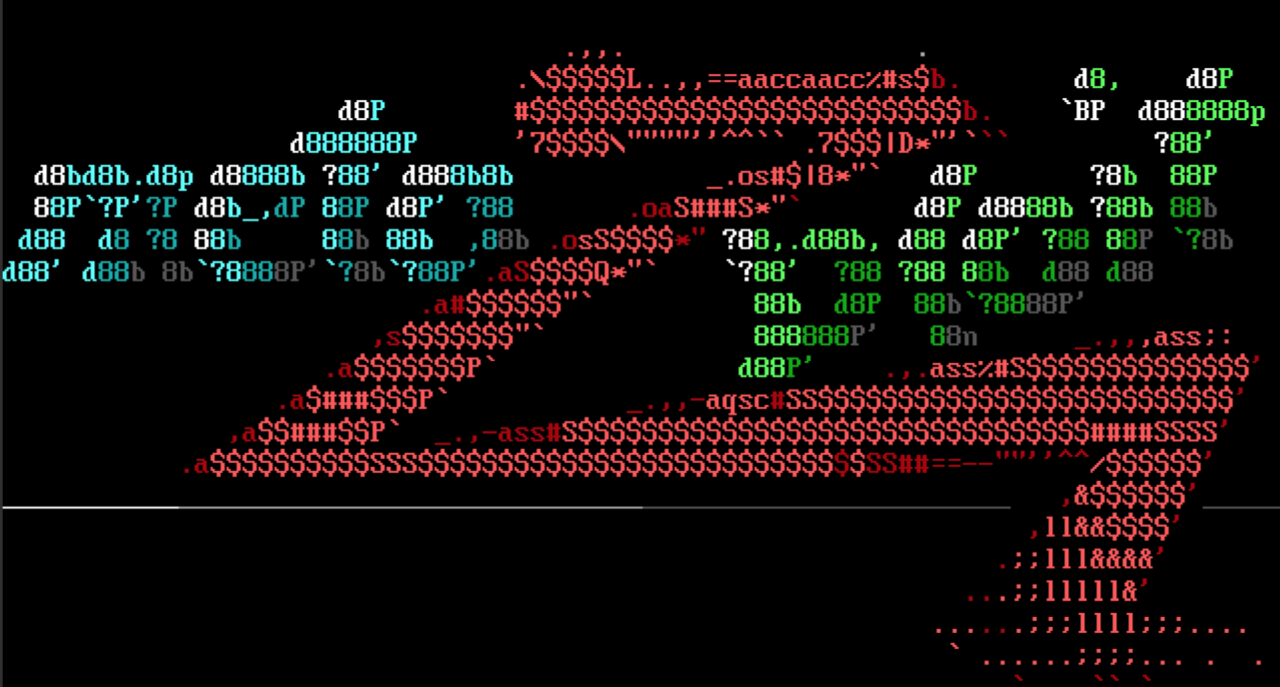
metasploit-framework/documentation/modules/payload/linux/x86/meterpreter/reverse_tcp.md at master · rapid7/metasploit-framework · GitHub

SANS Institute on X: "Metasploit Cheat Sheet 2 of 2 Learn "Metasploit Kung Fu for Enterprise Pen Testing" VEGAS - http://t.co/dANRxZe6pG http://t.co/xr2VBa4kq2" / X

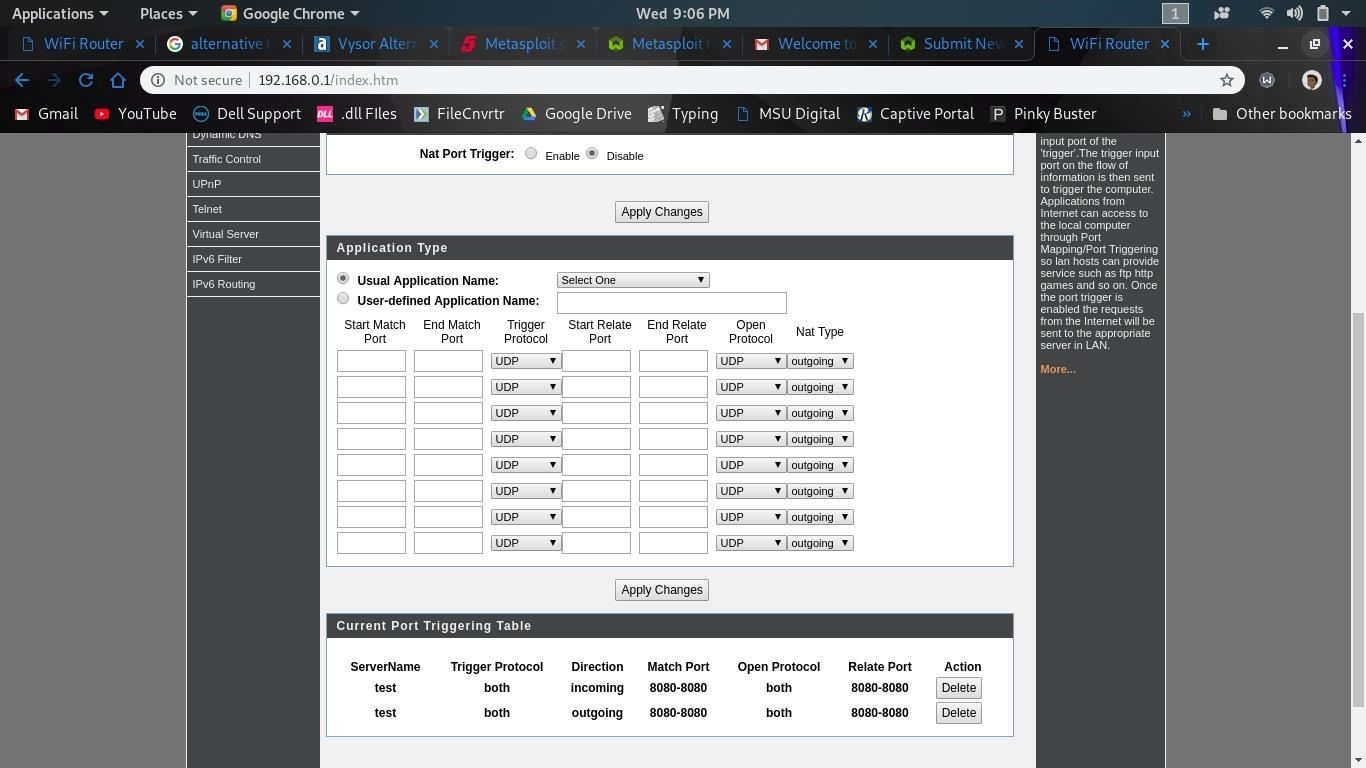
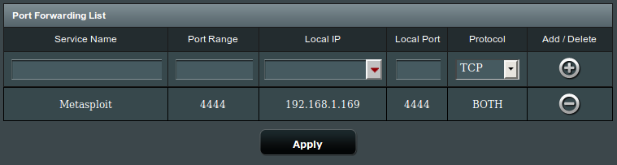
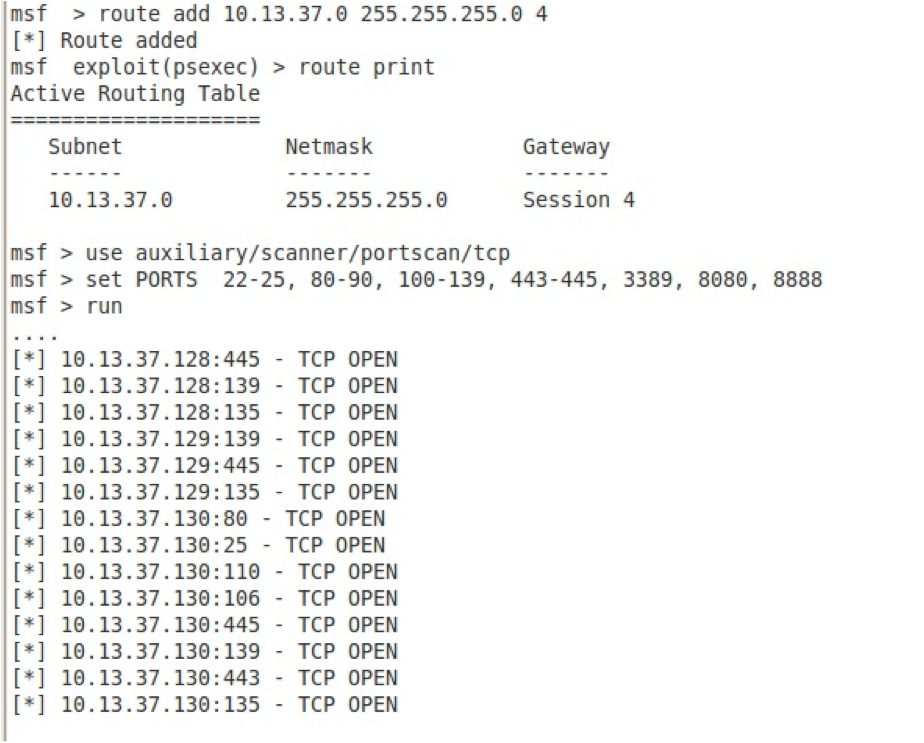
Network topology for generating exploit traffic. Attacker VM running... | Download Scientific Diagram